This article describes some basic Group Polices to get you started configuring RDS Server.
Preparation
Create OU for RDS Server in Active Directory. Create security group for users who will use Remote Desktop Host (i.e. RDS Users). Create GPO (i.e. RDS Server Lock Down). In Security Filtering delete Authenticated Users, add RDS Server Computer Account, and the security group created in previous step.
Configure users who can connect to the server remotely:
Log in to RDS Server >>> Run >>> control system >>> Remote Settings >>> Remote tab >>> Select users >>> Delete any groups/users >>> Add security group for RDS users
Disable Server Manager Pop Up at user log on:
On RDS Server open Task Scheduler. Navigate to Task Scheduler Library\Microsoft\Windows\Server Manager. Disable task “ServerManager” which triggers at log on of any user.
Some group policies might not be available in your group policy manager. You will need to add Administrative Templates for the Windows 8.1 and Windows Server 2012 R2: see Adding Windows 8.1 and Server 2012 R2 Administrative Templates.
Configure Group Policy for RDS Server Lock Down
Loopback Processing
[Computer Configuration\Policies\Administrative Templates\System\Group Policy]
Configure user Group Policy loopback processing mode: Enable – Merge
This policy setting directs the system to apply the set of Group Policy objects for the computer to any user who logs on to a computer affected by this setting. It is intended for special-use computers, such as those in public places, laboratories, and classrooms, where you must modify the user setting based on the computer that is being used.
If you enable this setting, you can select one of the following modes from the Mode box:
“Replace” indicates that the user settings defined in the computer’s Group Policy Objects replace the user settings normally applied to the user.
“Merge” indicates that the user settings defined in the computer’s Group Policy Objects and the user settings normally applied to the user are combined. If the settings conflict, the user settings in the computer’s Group Policy Objects take precedence over the user’s normal settings.
Disable Control Panel Items
[User Configuration\Policies\Administrative Templates\Control Panel]
Hide specified Control Panel items: Enable
This setting allows you to display or hide specified Control Panel items, such as Mouse, System, or Personalization, from the Control Panel window and the Start screen. The setting affects the Start screen and Control Panel window, as well as other ways to access Control Panel items, such as shortcuts in Help and Support or command lines that use control.exe. This policy has no effect on items displayed in PC settings.
If you enable this setting, you can select specific items not to display on the Control Panel window and the Start screen.
To hide a Control Panel item, enable this policy setting and click Show to access the list of disallowed Control Panel items. In the Show Contents dialog box in the Value column, enter the Control Panel item’s canonical name. For example, enter Microsoft.Mouse, Microsoft.System, or Microsoft.Personalization.
Add following items to the disallowed Control Panel items:
Microsoft.AdministrativeTools
Microsoft.AutoPlay
Microsoft.ActionCenter
Microsoft.ColorManagement
Microsoft.DefaultPrograms
Microsoft.DeviceManager
Microsoft.EaseOfAccessCenter
Microsoft.FolderOptions
Microsoft.iSCSIInitiator
Microsoft.NetworkAndSharingCenter
Microsoft.NotificationAreaIcons
Microsoft.PhoneAndModem
Microsoft.PowerOptions
Microsoft.ProgramsAndFeatures
Microsoft.System
Microsoft.TextToSpeech
Microsoft.UserAccounts
Microsoft.WindowsFirewall
Microsoft.WindowsUpdate
Microsoft.DateAndTime
Microsoft.RegionAndLanguage
Microsoft.RemoteAppAndDesktopConnections
Install Application On Remote Desktop Server
Java
Flash Player
Remove Administrative Tools and Powershell
Restrict access to Administrative tools
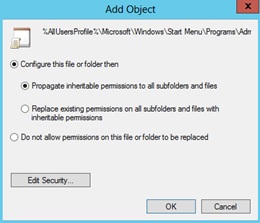
- Open RDS Lock Down Group Policy.
- Navigate to Computer Configuration >>> Policies >>> Windows Settings >>> Security Settings
- Right click on File System, choose Add File… .
- In the Add a file or folder window, put %AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\Administrative Tools in the Folder field and click OK.
- On the next window Database Security for %AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\Administrative Tools\Server Manager.lnk remove Users and check that Administrators have Full Access
- On the Add Object window choose Configure this file or folder then Propagate inheritable permissions to all subfolders and files. Click OK.
- Do the same for PowerShell shortcut (+ delete Creator Owner in database security): %AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\System Tools\Windows PowerShell.lnk
- Do the same for Server Manager shortcut: %AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\Administrative Tools\Server Manager.lnk
File Explorer Configuration
[User Configuration\Policies\Administrative Templates\Windows Components\File Explorer]
Enable – Restrict A, B, C and D drives only: Hide these specified drives in My Computer
This policy setting allows you to hide these specified drives in My Computer. This policy setting allows you to remove the icons representing selected hard drives from My Computer and File Explorer. Also, the drive letters representing the selected drives do not appear in the standard Open dialog box. If you enable this policy setting, select a drive or combination of drives in the drop-down list.
Enable – Remove Hardware tab
This setting removes the Hardware tab from Mouse, Keyboard, and Sounds and Audio Devices in Control Panel. It also removes the Hardware tab from the Properties dialog box for all local drives, including hard drives, floppy disk drives, and CD-ROM drives. As a result, users cannot use the Hardware tab to view or change the device list or device properties, or use the Troubleshoot button to resolve problems with the device.
Enable – Hides the Manage item on the File Explorer context menu
Removes the Manage item from the File Explorer context menu. This context menu appears when you right-click File Explorer or My Computer.
Enable – Remove Security tab
Removes the Security tab from File Explorer. If you enable this setting, users opening the Properties dialog box for all file system objects, including folders, files, shortcuts, and drives, will not be able to access the Security tab. As a result, users will be able to neither change the security settings nor view a list of all users that have access to the resource in question.
Disable Registry Modification
[User Configuration\Policies\Administrative Templates\System]
Enable – Prevent access to registry editing tools
Disables the Windows registry editor Regedit.exe. If you enable this policy setting and the user tries to start Regedit.exe, a message appears explaining that a policy setting prevents the action.
Configure Windows Installer and Windows Updates
[Computer Configuration\Policies\Administrative Templates\Windows Components\Windows Installer]
Enable: Prevent users from using Windows Installer to install updates and upgrades
This policy setting prevents users from using Windows Installer to install patches. If you enable this policy setting, users are prevented from using Windows Installer to install patches. Patches are updates or upgrades that replace only those program files that have changed. Because patches can be easy vehicles for malicious programs, some installations prohibit their use.
Enable Always: Turn off Windows Installer
This policy setting restricts the use of Windows Installer. If you enable this policy setting, you can prevent users from installing software on their systems or permit users to install only those programs offered by a system administrator. You can use the options in the Disable Windows Installer box to establish an installation setting.
[Computer Configuration\Administrative Templates\Windows Components\Windows Update]
Enable: Do not display ‘Install Updates and Shut Down’ option
This policy setting prevents users from using Windows Installer to install patches. If you enable this policy setting, users are prevented from using Windows Installer to install patches. Patches are updates or upgrades that replace only those program files that have changed. Because patches can be easy vehicles for malicious programs, some installations prohibit their use.
[Computer Configuration\Administrative Templates\Windows Components\Windows Update]
Enable: Do not display ‘Install Updates and Shut Down’ option
This policy setting allows you to manage whether the ‘Install Updates and Shut Down’ option is displayed in the Shut Down Windows dialog box.
Disable: Allow non-administrators to receive update notifications
This policy setting allows you to control whether non-administrative users will receive update notifications based on the “Configure Automatic Updates” policy setting.
Additional Policies
[Computer Configuration\Policies\Administrative Templates\Windows Components\Remote Desktop Services\Remote Desktop Session Host\Session Time Limits]
Enable (i.e. 30 minutes): Set time limit for disconnected sessions
You can use this policy setting to specify the maximum amount of time that a disconnected session remains active on the server. By default, Remote Desktop Services allows users to disconnect from a Remote Desktop Services session without logging off and ending the session.
When a session is in a disconnected state, running programs are kept active even though the user is no longer actively connected. By default, these disconnected sessions are maintained for an unlimited time on the server.
If you enable this policy setting, disconnected sessions are deleted from the server after the specified amount of time. To enforce the default behavior that disconnected sessions are maintained for an unlimited time, select Never. If you have a console session, disconnected session time limits do not apply.
[Computer Configuration/Policies/Administrative Templates/Windows Components/Remote Desktop Services/Remote Desktop Connection/Remote Desktop Session Host/Session Time Limits]
Set time limit for logoff of RemoteApp sessions: Enable (i.e. logoff delay 1 hour)
This policy setting allows you to specify how long a user’s RemoteApp session will remain in a disconnected state after closing all RemoteApp programs before the session is logged off from the RD Session Host server.
By default, if a user closes a RemoteApp program, the session is disconnected from the RD Session Host server, but it is not logged off.
If you enable this policy setting, when a user closes the last running RemoteApp program associated with a session, the RemoteApp session will remain in a disconnected state until the time limit that you specify is reached. When the time limit specified is reached, the RemoteApp session will be logged off from the RD Session Host server. If the user starts a RemoteApp program before the time limit is reached, the user will reconnect to the disconnected session on the RD Session Host server.
If you disable or do not configure this policy setting, when a user closes the last RemoteApp program, the session will be disconnected from the RD Session Host server but it is not logged off.
Note: This policy setting appears in both Computer Configuration and User Configuration. If both policy settings are configured, the Computer Configuration policy setting takes precedence.
[Computer Configuration/Policies/Administrative Templates/Windows Components/Remote Desktop Services/Remote Desktop Connection/Remote Desktop Session Host/Session Time Limits]
Set time limit for active but idle Remote Desktop Services sessions: Enable ( i.e. 1 hour)
This policy setting allows you to specify the maximum amount of time that an active Remote Desktop Services session can be idle (without user input) before it is automatically disconnected.
If you enable this policy setting, you must select the desired time limit in the Idle session limit list. Remote Desktop Services will automatically disconnect active but idle sessions after the specified amount of time. The user receives a warning two minutes before the session disconnects, which allows the user to press a key or move the mouse to keep the session active. If you have a console session, idle session time limits do not apply.
If you disable or do not configure this policy setting, the time limit is not specified at the Group Policy level. By default, Remote Desktop Services allows sessions to remain active but idle for an unlimited amount of time.
If you want Remote Desktop Services to end instead of disconnect a session when the time limit is reached, you can configure the policy setting Computer Configuration\Administrative Templates\Windows Components\Remote Desktop Services\Remote Desktop Session Host\Session Time Limits\End session when time limits are reached.
[User Configuration/Policies/Administrative Templates/Start Menu and Taskbar]
Go to the desktop instead of Start when signing in or when all the apps on a screen are closed: Enable
This policy setting allows users to go to the desktop instead of the Start screen when they sign in, or when all the apps on a screen are closed. This policy setting applies to all versions of Windows, and versions of Windows Server with the Desktop Experience installed.
If you enable this policy setting, users will always go to the desktop when they sign in, or when all the apps on a screen are closed.
[User Configuration/Policies/Administrative Templates/Start Menu and Taskbar]
Remove the Action Center icon: Enable
This policy setting allows you to remove the Action Center from the system control area.
If you enable this policy setting, the Action Center icon is not displayed in the system notification area.
If you disable or do not configure this policy setting, the Action Center icon is displayed in the system notification area.
[User Configuration/Policies/Administrative Templates/Windows Components/Windows Update]
Remove access to use all Windows Update features: Enable (0 = Do not show any notifications)
This setting allows you to remove access to Windows Update.
If you enable this setting, all Windows Update features are removed. This includes blocking access to the Windows Update Web site at http://windowsupdate.microsoft.com, from the Windows Update hyperlink on the Start menu, and also on the Tools menu in Internet Explorer. Windows automatic updating is also disabled; you will neither be notified about nor will you receive critical updates from Windows Update. This setting also prevents Device Manager from automatically installing driver updates from the Windows Update Web site.
If enabled you can configure one of the following notification options:
0 = Do not show any notifications
This setting will remove all access to Windows Update features and no notifications will be shown.
1 = Show restart required notifications
This setting will show notifications about restarts that are required to complete an installation.
[User Configuration/Policies/Administrative Templates/Windows Components/File Explorer]
Remove CD Burning features: Enable
This policy setting allows you to remove CD Burning features. File Explorer allows you to create and modify re-writable CDs if you have a CD writer connected to your PC.
If you enable this policy setting, all features in the File Explorer that allow you to use your CD writer are removed.
If you disable or do not configure this policy setting, users are able to use the File Explorer CD burning features.
Note: This policy setting does not prevent users from using third-party applications to create or modify CDs using a CD writer.
[User Configuration/Policies/Administrative Templates/Windows Components/File Explorer]
Prevent access to drives from My Computer: Enable (choose the drives)
Prevents users from using My Computer to gain access to the content of selected drives.
If you enable this setting, users can browse the directory structure of the selected drives in My Computer or File Explorer, but they cannot open folders and access the contents. Also, they cannot use the Run dialog box or the Map Network Drive dialog box to view the directories on these drives.
To use this setting, select a drive or combination of drives from the drop-down list. To allow access to all drive directories, disable this setting or select the “Do not restrict drives” option from the drop-down list.
Note: The icons representing the specified drives still appear in My Computer, but if users double-click the icons, a message appears explaining that a setting prevents the action.
Also, this setting does not prevent users from using programs to access local and network drives. And, it does not prevent them from using the Disk Management snap-in to view and change drive characteristics.
[User Configuration/Policies/Administrative Templates/Windows Components/Credentials User Interface]
Do not display the password reveal button: Enable
This policy setting allows you to configure the display of the password reveal button in password entry user experiences.
If you enable this policy setting, the password reveal button will not be displayed after a user types a password in the password entry text box.
If you disable or do not configure this policy setting, the password reveal button will be displayed after a user types a password in the password entry text box.
By default, the password reveal button is displayed after a user types a password in the password entry text box. To display the password, click the password reveal button.
The policy applies to all Windows components and applications that use the Windows system controls, including Internet Explorer.
[User Configuration/Policies/Administrative Templates/Windows Components/AutoPlay Policies]
Turn off Autoplay: Enable (CD-ROM and removable media drives)
This policy setting allows you to turn off the Autoplay feature.
Autoplay begins reading from a drive as soon as you insert media in the drive. As a result, the setup file of programs and the music on audio media start immediately.
Prior to Windows XP SP2, Autoplay is disabled by default on removable drives, such as the floppy disk drive (but not the CD-ROM drive), and on network drives.
Starting with Windows XP SP2, Autoplay is enabled for removable drives as well, including Zip drives and some USB mass storage devices.
If you enable this policy setting, Autoplay is disabled on CD-ROM and removable media drives, or disabled on all drives.
This policy setting disables Autoplay on additional types of drives. You cannot use this setting to enable Autoplay on drives on which it is disabled by default.
If you disable or do not configure this policy setting, AutoPlay is enabled.
Note: This policy setting appears in both the Computer Configuration and User Configuration folders. If the policy settings conflict, the policy setting in Computer Configuration takes precedence over the policy setting in User Configuration.
[User Configuration/Policies/Administrative Templates/Windows Components/Remote Desktop Services/Remote Desktop Connection]
Do not allow passwords to be saved: Enable
Controls whether a user can save passwords using Remote Desktop Connection.
If you enable this setting the credential saving checkbox in Remote Desktop Connection will be disabled and users will no longer be able to save passwords. When a user opens an RDP file using Remote Desktop Connection and saves his settings, any password that previously existed in the RDP file will be deleted.
If you disable this setting or leave it not configured, the user will be able to save passwords using Remote Desktop Connection


Pingback: Windows Server 2012 RDS
Hi, i have reading out and i will definitely bookmarrk your site, just wanted to say i liked this article.
Great article, thank you for sharing this information.
I enjoy the efforts you have put in this, regards for all the great posts.
so how do you restrict access to C:\
when a user can right click on the icon on start menu, and then select open file location – despite the drive being hidden.
You can use “Prevent access to drives from My Computer” in User Configuration\Administrative Templates\Windows Components\Windows Explorer.
Prevents users from using My Computer to gain access to the content of selected drives.
If you enable this policy, users cannot view the contents of the selected drives in My Computer and Windows Explorer. Also, they cannot use the Run dialog box, the Map Network Drive dialog box, or the Dir command to view the directories on these drives.
To use this policy, select a drive or combination of drives from the drop-down list. To allow access to all drive directories, disable this policy or select the Do not restrict drives option from the drop-down list. http://technet.microsoft.com/en-us/library/cc978514.aspx
This article was exactly what I was looking for. I appreciate you taking the time and effort in creating it and passing your knowledge on.
How will this affect administrators who still require full control? Is there a way to have them exempt from these policies?
I usually create a security group (i.e. RDS Users) and assign this GPO to this group. Administrator is not a member of this group and therefore the group policy is not applied to this account.
In your first paragraph when you say “add RDS Server Account” What account are you referring to?
Hi Duane,
It is a computer account of the RDS Server in AD.
Thank you so much – It was very helpful to find all this information in one place. It was a great starting point for locking down my first 2012 RDS.
Did anyone else experience since Update 1 for 8.1/2k12r2 that RDS users can still see all administrative tools from the metro menu, or through metro search?
In my case, they can even browse some of the informative eventlogs, provided they know how to get there.
Hi, I’m having trouble getting these policies to work. It seems that when enabled the GPO isn’t actually working for me. I have a “Groups” OU with my “RDSusers” and “RDSFarm (for my Session Host servers, 2 of them)” security groups inside. I created the policy above with respect to turning off the control panel and locking down PowerShell, Server Manager, and Administrative Tools. I have filtered according to the groups I mentioned above and have the policy linked the the parent OU that contains the group OU. When logging in as a user in the RDSusers to either of the servers I still have access to everything. Quick notes:
-I log in using a round robbin DNS, “rdsfarm”
-Loopback processing was not an available option for me
I am running Server 2012 R2.
Thanks!
Hi Mike,
Group Policy should be applied to the RDS Farm OU (Computers). Loopback policy in Server 2012 is in the following location: Computer Configuration\Policies\Administrative Templates\System\Group Policy
Setting\Configure user Group Policy loopback processing mode
Bam! Just the info for which I was looking. Thanks for taking the time to write this up!
One question – How do I ensure that this GPO only affects users when they log onto the RDS server and NOT when they log onto their local computers within the domain. There is some crossover between who work locally, but also need remote access from time to time. I’ve obviously added these people to my RDS Users OU with the GPO linked so that they can log on to terminal sessions. Any insight is appreciated.
Thanks!
Ben
Hi Ben,
You can create OU in Active Directory (i.e. RDS Servers). Put computer account to this OU and then create a “Lockdown RDS” Group Policy with Loopback policy configured. Delete “Authenticated Users” from Group Policy Security Filtering for “Lockdown RDS” GPO. Add RDS Server computer account and your “RDS Users” security Group. This way users who login to RDS Server will receive the Computer and User policies configured for the RDS server.
I love this article! Straight, forward and to the point! I have a question. Is there anyway to lock down a group of users from seeing a specific application? thanks, Nick
DO NOT USE “merge” in the Loopback Processing. Normally the guys that manage the clients don’t think on the side effects on the RD-Servers. USE “replace”
Thank you so much. Very useful article on getting started with RDS. I appreciate the sharing.
Just want to say this is the best written example of this process I have seen. Your approach to dealing with this is refreshing compared to the dens TechNet stuff which tends to spend more time linking other KB’s than actually dealing with the issue at hand. Thanks for the work.
A very detailed, yet very useful guide. I have downloaded and saved in my dropbox for future reference.
Thank you for taking the time to compile and share this information.
My client will be logging on to their 2012 RDS server for the first time tomorrow and previously I have not implemented these lock downs because I did not want to deal with digging through all the items. You have already done this for me and everyone else. Bravo!
Thanks.
Brilliant page, setup straight forward.
Only problem I’ve got is that users now cant see the D:,& D: drives on there own machine, so presume it’s applied the policy to there local machine as well as the RDS, is there a way to only apply on the RDS?
have i done something wrong something wrong?
Brilliant page works like a treat on the RDS.
My only problem is that its applying to the users local PC, so the have lost access to there local c: drive?
Any idea’s what to do or what i have done wrong?
Hi Aaron,
Did you create a separate Organisational Unit in Active Directory for your terminal server? I usually create OU (i.e. RDS Servers) and apply GPO to it.
Thanks for your help again,
I had created an OU for RDS servers and had the RDS server in there, but for some reason when i created the GPO i put it above this group so was aplying to all users and all computers. woops!
Glad that you have found the problem
Grrreat work here!…. Gracias……2 questions, First, how do i prevent RDS users from launching the Start button or even it should NOT be visible to them. 2. when they log in….. launch the specified app and give them ability to print….. Thanks..
Hi Jawad. May be you should consider publishing apps via RDWeb?
Thanks for taking time to make this GPO guide for RDS on W2012R2 🙂
It was really helpful.
This is a great walk-through, and exactly what I was looking for to lock down the users within a new RDS host. However I am personally having issues with the implementation of such.
I have a single Win2012R2 server stood up as the sole DC as well as the RDS host for a small business. The GPO (created as noted above) is targeting specifically the user group who needs RDS access as well as the server’s account as stated. This works great on the users I am allowing access to, but it goes a little out of scope…
When I deploy this RDS GPO to the same OU container as the Domain Controller GPO – once again, single server domain; this policy is attaching on the Domain/Enterprise Admin groups as well when I do a resultant set of policy. This is even when I am explicitly denying ‘Apply Policy’ in the Delegation screen for Domain/Enterprise Admins within the RDS GPO.
Any suggestions would be great as I am scratching my head why the policy is ignoring the security filter as well as the explicit Deny.
Hi Gil,
That’s the reason why RDS should not be installed on DC. But you probably know that already.
The Computer Configuration part of the Lockdown GPO will be applied regardless who is logging in. Since it is applied to a computer, not user. If you check the RSOP you would see that only Computer Configuration part of a Lockdown GPO is applied.
The User Configuration part will not be applied. Since only the members of the RDS Users group get the user configuration settings of the GPO.
Hi Gil,
In that case, you have yet another option.
If you’re using a single server and have Windows Server 2012, than you most certainly have a legal license.
That means that you can install the free Hyper-V on the physical machine and use the two (Server Standard) licenses for two virtual machines: one for your multi-purpose server (DC, file/print, etc.) and the other one for a dedicated RDS host.
This way, you make better use of your hardware (provided you have decent hardware) and better use of your security setup, since you don’t allow your users to actually work on your DC or file/print/application server (which I wouldn’t recommend anyway.)
Downside to all this is that you already have a working system, so you’d have to backup and reinstall to have this working, but it would be well worth it if you did.
Consider this option if you want to limit your headaches.
Hi George,
Thanks for sharing your ideas. I agree that this would have been a better design to have a DC and RDS separated. Especially taking into account that Windows Server 2012 Standard comes with a license for 2 virtual machines.
Hi! Thanks for the article. I have one question. If you restrict access to the C:\ drive that users do not have access to the folder “Documents”.
Hi Pavel,
How do you want to restrict users? The above policy (Restrict A, B, C and D drives only: Hide these specified drives in My Computer) is not restricting but rather hiding the drive from My Computer. Users still can access the C Drive (i.e. enter a “C:\” in Windows Explorer).
Hi!
Awesome article made my RDS lock down very easy.
But I have a question for you? How do I remove access to “System Tools” from the Metro UI on 2012 R2?
Cant seem to find anything in GPO or on local machine? Or is this done on my Build before it becomes a RDS server? Like when I am building a sysprep’d server to rollout?
Andy
Hi Andy,
What ‘System Tools’ do you refer to? Do you mean ‘Administrative Tools’? If yes please see ‘Remove Administrative Tools and Powershell’ section. If you do not want users to see the ‘Administrative Tools’ tile in metro UI you need to customise the Metro UI. Please refer to this article: http://microsoftplatform.blogspot.com.au/2013/06/predefining-and-customizing-modern-ui.html
Thanks for this Great article!
I am trying to keep users from the Metro Start, they just need one icon on the desktop and a way to Log Off.
I read the link in your last reply on Nov 3 – 2014 but not sure if that will do what I am trying. I would really like just a Blank Screen when they click the Start and go to the Metro Start, but if the user starts to type, I do not want it to start the Search… is there a way to Lock the Search?
Thanks
Michael
Thank you,
There are some great tips specific to 2012 that I very much appreciate. In my earlier terminal services deployments. I had enable in GP a setting to not show computers near me to prevent users from seeing the network resources in our domain. This no longer works. Do you now of a setting that will remove NETWORK from the file explorer?
Thank you
Hi Brian,
Try the following link http://www.emware.nl/articles/remove-the-network-link-from-windows-explorer.html
pls. i need assistance for this problem if your system is complaining about this what will you do:
1. it will bring a command to enter the keyboard language.
2. when i select keyboard language another two message will appear
(a) hard disk cannot repair because administrative drive is lock (b) Recovery tools
Thanks for the article. Very helpful.
I have configured our environment now and it has been running wonderfully.
Could you advise how I can turn off the ability of Domain Admins (or selected domain admins by adding them to an OU or Group) to restart or shutdown the Session Host itself, but retain their ability to initiate other systems (like CMD, browsing back to C and all other drives and network browsing etc)?
Although they should know to be careful – I would like to remove all possiblity that IT department staff don’t accidently restart or shutdown a Session Host when they are logged in as themselves?
Thanks
hi,
It’s a great job of this artical. one question about the taskbar, Can I put the “logoff”, and some program icon(like, WORD, EXCEL….) in the TaskBar through GPO for every RDS users?
B.RGDS
MT
You amazing man!!
thank you so much
Thank you for all the great info here, i have configured my 2012 R2 RDS & will be make public very soon i will post back with the result,
Hi, how are you? Thanks for this post, this may come in handy soon.
Just one question for you, I have users getting their custom pc settings put back to the default after they log in and out of a remote terminal session.
For example, the cursor blink rate is set to fast for all users except the administrator on the remote server. When users change it to a speed they prefer and logs off then logs back in, it changes back to fast.
Is this a permission issue? Or am I missing something?
Appreciate any help, cheers
Great article. Very helpful.
Unfortunately, I applied this GPO to a Win2012 R2 RDSH without first preventing it from applying to Administrator.
Now Adminstrator cannot open Administrative Tools and only certain Control Panel icons are present.
Is there a way to reverse all of these changes so that the Administrator account has access to Admin Tools, etc?
Many thanks for a very helpful article.
You can unlink or disable the GPO from the server and reboot the SH server.
Re-read this great post and make sure you do the step with ensuring the Group Policies only apply to certain user and computers.
Hi,
I’d like to start by saying that this is a very good article, and thank you for posting it.
Not sure what I am doing wrong, but the GPO doesn’t seem to have any impact whatsoever on RemoteApp or Remote Desktop sessions. I followed all the instructions, and the RemoteApp user can create folders and save files both to the RD Session host C: drive AND to the local C: drive although drives are unchecked in the client settings of the collection. Running gpresult /v shows no sign of the GPO I defined. I’m sure it’s probably one thing I’m not doing as everyone here was able to make it work.
The structure is:
AD-DS – Windows 2012
RD Broker – Windows 2012
RD Session Host Windows 2012 R2
Created an OU for the RD Session Hosts
Created a security group G-Excel Users
Followed instructions in the Preparation part
Linked the GPO to both the security group and the RD Session Host OU
waited for more than 90 minutes
The Excel user can also use MSTSC to remote desktop and has access to C drive of the RD Session host.
When running the Excel from RDWEB – same access – using the File -> Save As it’s possible to create folders under C: drive (both local PC and the server itself) plus running any application from the Windows explorer address bar, like CMD, notepad, etc.
I don’t seem to find what’s missing.
Hopefully you can give me the hint that will make it work.
Thanks a lot !
Shimon.
Technet Forum post – https://social.technet.microsoft.com/Forums/windowsserver/en-US/211a1013-001b-4791-b835-a7315e699611/rds-2012-r2-how-do-i-lockdown-access-to-local-computer-management-and-windows-backup-via-group?forum=winserverTS
I hope you can help, I can’t find a way to lockdown Computer Management and Windows Server Backup. These are both available via the Win-X shortcut and I would like to lock them down.
Hope you can help.
Terry
Hi,
I have made some changes and it seems that GPOs are working but right now I have the following behavior:
Remote Desktop Session end users can create files and folders ONLY on their desktop. Not even in their Documents folder. I could live with that, but the annoying problem is that when they do create a folder on their desktop – they can’t open it or save anything into it…
I have defined UPD for the collection, and implemented the following GPOs:
– Prevent access to the command prompt
– Remove Lock Computer
– Hide these specified drives in My Computer – A, B, C, D
– Prevent access to drives from My Computer – C
– Prevent Users from adding files to the root of their Users Files folder
Any logical explanation for this behavior, and possibly a solution ?
Thanks,
Shimon.
Hi Shimon,
I guess the problem is that you have enabled – “Prevent access to C drive”
Very helpful. Thanks!
Great help for setting up GPO’s on an new Server . I never have all the Little things in my head. Now at this place i can look everytime i do a new TS .. Thank you very much
Real helpful blog, thank you.
I have a TS set up across 4 servers.
Gateway
Broker
Session Host 1
Session Host 2
These GPOs should be applied to the Session Hosts correct?
Thanks.
Hi Malcolm,
Yes apply this GPO to RDSH.
Thanks…and the GPO is created and managed on the RDSH or does that not matter?
(sorry for the silly questions) #newbie
Hi Malcolm.
The GPO is created/managed from Group Policy Management on your Domain Controller. Create Organisational Unit in Active Directory for your RDSH servers and attach the GPO to this Organisational Unit.
This guide has helped me out tremendously. Thanks.
A couple things that are not working for me:
Disabling Server Manager: I have added the exceptions to Computer Configuration >>> Policies >>> Windows Settings >>> Security Settings and it doesn’t prevent a user from opening the Server Manager Software. I even went so far as to add the user group to the ACL and Deny access to the group that shouldn’t have access to it. I even deleted the local profile of the test account after making all of the GPO changes and it is still not working.
Here is a list of items I have changed the ACLs on:
%AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\Accessories\Windows PowerShell\Windows PowerShell (x86).lnk
%AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\Accessories\Windows PowerShell\Windows PowerShell.lnk
%AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\Administrative Tools
%AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\Administrative Tools\Server Manager.lnk
%AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\System Tools\Windows PowerShell.lnk
%SystemDrive%\Users\Default\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\Server Manager.lnk
%SystemRoot%\system32\ServerManager.exe
%SystemRoot%\System32\WindowsPowerShell\v1.0\powershell.exe
Powershell: I am using Software Restrictions because the above technique did not prevent our users from accessing the Powershell console. I need to finish this by preventing access to the ISE, since our users can still use the “Search” function.
I don’t seem to have everything available under Computer Management. I have no “file system” entries, a much shorter list of nodes. Are there more than one Computer Management console?
Thanks,
Jeff
Hi,
I’m having a RDS GW server (W2012R2), which points to 2 RDS W2012R2 (RDS1 and RDS2). Restricted users from accessing C-Drive, folder redirection, TS profile, etc.
Now I saw on a users desktop a Mozilla Firefox icon ( I only installed IE11 & Chrome as Admin), so I asked the user how he got that and told me he downloaded the app and installed. When promted for Admin credentials he left them blanc and clicked yes/continue. Same popup for Admin credentials and he presses cancel and the setup continues to install on his C:\users\%username%\Appdata\Local\ folder and creates a shortcut on the desktop for the current user (allowed to add icons to the desktop).
The same thing he did with Dropbox!
I’m doing the same under a test account as a User and Dropbox says after Cancelling the Admin prompt “Dropbox can be installed without Administrator rights, continue?” and it installs in de C:\users\%username%\Appdata\Local\ folder
Very strange that this is possible!?
Anyone the same problem?
Hi, my problem may be the same as Jeff’s. Under Computer Configuration >>> Policies >>> Windows Settings >>> Security Settings, I do not File System. I have seen this edit suggestion on many sites, but this is the first time I have seen anyone else with this issue.
Hoping someone has a suggestion.
John
Sorry, missed out a couple of words in original post – should have read…
Hi, my problem may be the same as Jeff’s. Under Computer Configuration >>> Policies >>> Windows Settings >>> Security Settings, I do not have the key File System. I have seen this edit suggestion on many sites, but this is the first time I have seen anyone else with this issue.
Hoping someone has a suggestion.
John
Hi John,
Are you using Group Policy Management mmc? This setting is not present in the Local Computer Policy object.
Greetings,
-Thank You- for this informative article, most appreciated.
Using your guide, I was able to ‘lock down’ an RDS session to ‘traditional’ (pre-Win8) workstation functionality..
But ‘Metro’ -> “Charms” was an issue: server utililies in [Search].
A question: Is there a way to control or disable [Search] in Charms, via GPO, or another method, just short of a physical ‘hack’ / removing the files located at:
%windir%\SystemResources\Windows.UI.Search\XAMLTemplates ?
Removing the files effectively disables [Search] in Metro->Charms, but it is a ‘global’ mod. / affects all users on the system.
Would appreciate any feedback on other options,
Thanks, Robert
Hello,
I followed your post and everything is working like it should for normal users. Unfortunatly for Administrator users we have problems with the file restrictions. For some reason it keeps on saying that domain admins do not have permission to access the files when they log on.
Now when they click on it once for adminsitrative tools it gives them that pop up with the prompt to continue and actually give it the access.
Any way to resolve this so that my domain admins do not get the annoying pop up everytime they log on?
The exact message of the popup:
This file does not have a program associated with it for performing this action. Please install a program or, if one is already installed, create an association in the Default Programs control panel.
C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Administrative Tools\ and further as that I can’t see. But when I browse to it, it shows that Server Manager.lnk can’t be started from the shortcut anymore.
Any ideas how to resolve this little annoying issue? Even new domain admins get that popup.
Thanks.
Hi,
Please make sure that the GPO is applied to your specific group (i.e. RDS users), not to Authenticated Users group.
Thanks for this – it’s a good list.
I think the main thing to remember in an environment with terminal server and desktops is to use loopback policy so users get the right policy for the right environment.
Is there any way to lockdown users from open command prompt, but yes allow logon script and batch file to run?
This is what I’m looking for.
It would be easier to implement it if you would export your GPO and we could download it.
Or please send it to me per Mail.
Thank You
Great guide!
Is there any way to disable/remove the “Start” button from the desktop?
Very good article.. well explained. Thank you!
Thanks for posting.
One thing I can’t get to work is the hiding of the C:Drive in File Explorer. I still need my users to be able to browse network drives but when I apply the GPO stating Hide C: it prevents users from opening File explorer from the desktop. They can still open from the start menu app list though and if I pin file explorer from the app list to the task bar it opens fine.
Has anyone else experienced this?
I started with a blank GPO so don’t think there are any conflicts.
Hi
I also have the issue where many of my users login to a local domain joined workstation in addition to working externally on the RDS servers.
The problem is that i want the GPO to apply to users when they connect to the RDS farm, i do not want these restrictions like hiding C: drive and removing control panel items when they are working on their own local pc’s
I have created a security group called RDS Users and added the relevent people to it.
Some of these people have both a local pc and need to access the RDS Servers extenally.
I have also created an OU called RDS Servers and added the RDSH’s to it.
The GPO is only applied to the RDS Servers OU and RDS Users Security Group.
So the question is, how can i apply all the restrictions of this GPO which is exactly what i want but without also affecting users who login locally.
Cheers for any advice – Steve
Hi Steve.
“The GPO is only applied to the RDS Servers OU and RDS Users Security Group.” Do you mean Security Filtering of the group policy?
Please make sure that the actual GPO is under the OU where the RDS host/farm computer accounts located (“RDS Servers” OU).
Remove Administrative Tools and Powershell:
I put the settings in a GPO and apply this on a OU of the RDS servers.
The Server Manager icon is gone, Administrative Tools doesn’t work anymore but the Windows Powershell icon is still there.
What could be wrong?
I have the same issue.
One of the best MS articles I have seen (and I used to work for MS).
It would be great if there was a Starter GPO with these settings in it (hope I didn’t miss it).
Also…we deliver an application to customers via app services for legacy VB6 apps…is there a way to remove their ability to log into a desktop (they can only launch a remote app)?
Great article
Hello
We use Windows 2012.
I am looking to restrict certain applications for certain Admins. For example, I want to remove access to every administrative tool except NPS (network Policy Server) for Admin 1 and Admin 2, is this achievable? Thanks.
Hi Syed,
I think you should create security groups and use software restrictions policies.
is there any way to enable drag in drop for the users? or are these GPO locking that down too?
My 2012 R2 RDS server is hosted at a providers datacenter. I have a static VPN between the 2 sites and it works fine. As users begin to use the RDS server, they browse the Internet (80 & 443) out my providers firewall. Any way in windows to force them to come back across the VPN and browse out my firewall? My firewall has a tremendous amount of features and content filtering that my provider doesn’t offer.
Thank you!
This information made me really happy. I would like to add one more setting to enable.
User Policy/Administrative Templates/System/Ctrl+Alt+Del Options/Remove Task Manager
Admin,
Thanks for the write up!
In using this, I have a question as regards to Computer Configuration sections. Since the RDS computer is in the OU folder the gp policy applies to, won’t all users who login, including admins, have the Computer Policy section applied to their session? Since they are not in the security group, the user section of the gp policy will not apply to the, correct?
Hi O’Neal.
Since the RDS computer is in the OU folder the gp policy applies to, won’t all users who login, including admins, have the Computer Policy section applied to their session?
Yes. All Computer settings will be applied for all users including administrator. I need to update the article but did not have time to do this.
Basically recommendation is to apply as much settings as possible in User Configuration instead of Computer Configuration.
Since they are not in the security group, the user section of the gp policy will not apply to the, correct?
Administrators will not receive User Configuration settings since they are not members of the RDS Users group
I refer to this excellent document every time I build an RDS server. Thanks for this outstanding resource to the community!
Hi,
I have running RDS in a 2012 R2 infrastructure with latest patches.
The policy “Hide these specified drives in My Computer” doesn’t work with me.
User still can see C:
Can someone confirm that it still work?
Thanks for finally talking about >Lock Down Remote Desktop Services Server 2012 / RDS 2012 R2 | IT Blog <Liked it!
Pingback: Bulletproof RDS: 30 Ways to Secure Remote Desktop Services | CLOUDBITZ
Thanks for the article. I was cruising through it and then ran into some obstacles. I created the lockdown policy and have the group RDS Users and the Server (RDS-01) in security filtering. My Domain admin account is not a member of the RDS Users GPO, however, all the policies appear to still apply to my account? When I remove the server from the GPO none of the policies, including user policies work? I would sure like to lock down our RDS servers however I’d prefer not to have to remove the server from the policy every time we need to work on the server. I verified loopback processing, merge is enabled. Any ideas?
I am having this issue. When the user logs in and clicks start – they can see ‘Computer’. If they click computer there is ‘Network’. If they click ‘Network’ they can see all the machines on the network.
How do I hide computer and network from this view. At top it says system tools.
Hello,
One thing I can’t get to work is the hiding of the C:Drive in File Explorer. I still need my users to be able to browse network drives but when I apply the GPO stating Hide C: it prevents users from opening File explorer from the desktop. They can still open from the start menu app list though and if I pin file explorer from the app list to the task bar it opens fine.
Has anyone else experienced this?
I started with a blank GPO so don’t think there are any conflicts.
Great walk-through!
How does this apply to Windows 10 and 2012 R2 RDS? I followed your steps but GPO does not seem to be working as the user can still “see” everything they shouldn’t. (Server manager, Admin Tools)
Hi, have a requirement to only allow locked down File Explorer and other apps thru RDWeb. No RDP.
Env is Win 2016 DC edition.
If I just hide A B C D, it works but users can simply type C:\ and access the contents. But can see and edit their desktop, documents, etc. stored on the User profile disk.
And when I enable “Prevent access to drives from My Computer – A B C D”, it locks down everything Desktop, Document, etc. and users can no longer access their stuff in their profile disk (which resides on a network share). But i guess mounted under c:\users\\
Wondering what my options are.
If there is a way to block address bar in File explorer, would def. lock it down. But do not see that option in GP. Have already disabled Win+x keys.
Also Hide File Menu does not seem to work in Win 2016.
Any help/feedback is appreciated.
Reposting, not sure what happened…, if duplicate, please excuse…
Hi, have a requirement to only allow locked down File Explorer and other apps thru RDWeb. No RDP.
Env is Win 2016 DC edition.
If I just hide A B C D, it works but users can simply type C:\ and access the contents. But can see and edit their desktop, documents, etc. stored on the User profile disk.
And when I enable “Prevent access to drives from My Computer – A B C D”, it locks down everything Desktop, Document, etc. and users can no longer access their stuff in their profile disk (which resides on a network share). But i guess mounted under c:\users\\
Wondering what my options are.
If there is a way to block address bar in File explorer, would def. lock it down. But do not see that option in GP. Have already disabled Win+x keys.
Also Hide File Menu does not seem to work in Win 2016.
Any help/feedback is appreciated.